How Cloudflare's Security Overview Dashboard Prioritizes 10M+ Daily Security Insights
Cloudflare has introduced a new Security Overview dashboard designed to transform how security teams handle overwhelming amounts of data. By consolidating signals from various sources and applying intelligent prioritization, it turns millions of daily observations into clear, actionable items. This Q&A explores the dashboard's features, underlying technology, and practical benefits for incident response and risk management.
What is the Cloudflare Security Overview dashboard?
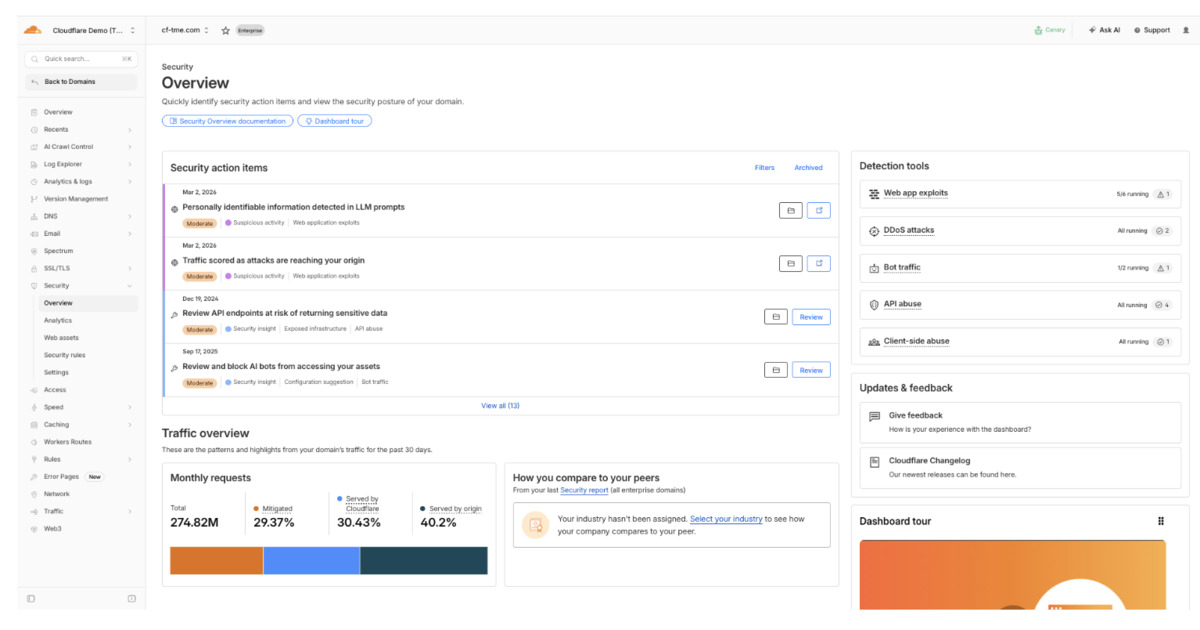
The Security Overview dashboard is a centralized hub that aggregates security alerts, logs, and events from across Cloudflare's network. It processes over 10 million insights each day, using machine learning and rule-based analysis to identify patterns and anomalies. Instead of presenting raw data, it prioritizes findings into a list of actionable tasks, enabling teams to focus on the most critical risks first. The dashboard leverages distributed checkers that run globally and real-time event processing to detect threats as they emerge. By reducing noise and highlighting what matters, it helps organizations respond faster to incidents and reduce the time spent on manual triage.
How does the dashboard process over 10 million daily insights?
Cloudflare's infrastructure spans over 300 data centers worldwide, with each point of presence running distributed checkers that continuously monitor traffic and security events. These checkers generate raw signals that are streamed into a real-time event processing pipeline. The pipeline correlates data across multiple dimensions—such as IP reputation, attack patterns, and user behavior—to produce aggregated insights. Every insight is assigned a severity score and grouped by type or source. With parallel processing and a scale-out architecture, the system can handle millions of events per second while maintaining low latency. This allows the dashboard to surface over 10 million actionable insights daily, updating in near real-time.
What are the main benefits for security teams using this dashboard?
Security teams often struggle with alert fatigue and scattered data. The Security Overview dashboard addresses these pain points by:
- Prioritizing risks: High-severity issues are surfaced first, reducing time to remediation.
- Consolidating signals: All sources (firewall logs, WAF alerts, rate limiting) appear in one view.
- Reducing investigation overhead: Built-in analytics and context eliminate the need to cross-reference multiple tools.
- Improving response efficiency: Teams can drill down from a summary to detailed event data directly.
As a result, analysts can resolve threats before they escalate, while also gaining insights into long-term trends for proactive defense.
How does integration with existing analytics workflows work?
The dashboard is designed to slot into existing security operations. It provides APIs to export prioritized action items to platforms like PagerDuty or SIEM tools. Within Cloudflare's ecosystem, it links directly to other dashboards (e.g., Analytics, Security Events) so users can pivot from a high-level finding to granular logs. The built-in analytics capabilities allow teams to create custom queries and save filters. For example, an administrator can set up a view that only shows DDoS-related insights from a specific time period. This integration reduces the need for manual data gathering and lets analysts focus on response rather than collection.
/presentations/game-vr-flat-screens/en/smallimage/thumbnail-1775637585504.jpg)
How does this dashboard differ from Cloudflare's previous security monitoring tools?
Earlier tools provided individual logs or aggregated stats, but required users to manually correlate signals across multiple tabs or APIs. The Security Overview dashboard is a departure from that model—it is purpose-built for prioritization. Instead of showing every event, it uses risk scoring to highlight only the most impactful ones. It also introduces the concept of "action items" with clear recommendations, such as "Enable rate limiting for endpoint X" or "Review IP block list for this region." Previously, such insights would have required custom scripts or deep expertise. The dashboard democratizes security intelligence, making it accessible to teams with varying skill levels.
What impact does real-time event processing have on threat detection?
Real-time processing allows the dashboard to reflect changes almost immediately. When a new attack pattern emerges—say, a burst of credential stuffing attempts—the distributed checkers flag it within seconds. The event processing pipeline updates the insight list, so analysts see the urgent spike without waiting for batch reports. This speed is critical for containing fast-moving threats like DDoS or brute-force attacks. Additionally, the real-time aspect enables the dashboard to provide ongoing situational awareness, not just post-incident analysis. Teams can set alerts for specific conditions and get push notifications, ensuring they never miss a critical shift in their security posture.
Related Articles
- 5 Essential Insights into Microsoft's Agent Framework for .NET Developers
- Effortlessly Convert Image Data to Excel Spreadsheets Using Data from Picture
- Unlocking Business Value with Enterprise AI Agents: Architecture, Real-World ROI, and Governance
- Mastering AI Agents in .NET: A Step-by-Step Guide
- 5 Key Linux App Updates That Shaped April 2026
- North Korean Hackers Infiltrate Axios: What Happened and How to Protect Your Systems
- How Countries Can Successfully Transition Away from Fossil Fuels: A Practical Roadmap
- Defending Against Supply Chain Attacks: How AI-Powered EDR Neutralized the Axios RAT Campaign