Breaking: Cybersecurity Shifts from Signature Matching to Context-Aware AI Intrusion Detection
In a major paradigm shift for network security, intrusion detection systems (IDS) are moving away from traditional signature-based matching toward machine learning and autonomous agents that assess behavior in context. This evolution is not incremental—it fundamentally changes how threats are identified, reducing false positives and catching novel attacks.
“We’re moving from ‘does this byte sequence match a known malware sample?’ to ‘does this sequence of actions make sense for this user, this device, this network?’” said Dr. Elena Voss, chief AI security researcher at CyberNova Labs. “That is a completely different, and far more scalable, problem.”
Industry insiders confirm that several leading cybersecurity firms are already deploying agentic AI—autonomous software agents that can make real-time decisions—in their IDS pipelines. These agents learn normal network patterns and flag anomalies without needing pre-configured signatures.
Background
Traditional signature-based detection relies on databases of known threat fingerprints. While effective against known malware, it fails against zero‑day exploits and polymorphic attacks that change their code to avoid detection. False positive rates also remain high because signatures cannot account for context.
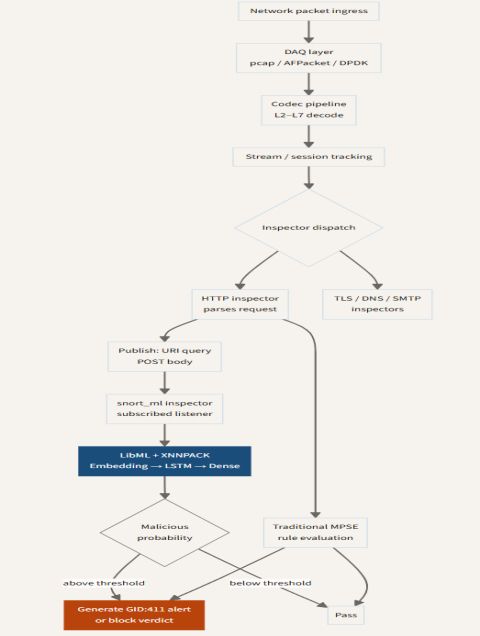
Machine learning (ML) models, especially deep learning, can analyze raw traffic features and identify subtle deviations. Agentic AI takes this further: autonomous agents not only detect but also decide on automated responses, such as isolating a compromised endpoint or blocking a suspicious data transfer.
The shift has been accelerated by the explosion of encrypted traffic and cloud environments, where static signatures are nearly useless.
What This Means
For security teams, the change promises a dramatic reduction in alert fatigue. Instead of thousands of signature matches that require manual triage, ML‑driven systems can filter by relevance, prioritizing incidents that truly indicate compromise.
“The real win is operational efficiency,” said Marcus Chen, CTO of SecuroTech. “A single agent can monitor an entire enterprise network and flag only the 0.1% of traffic that actually requires human investigation. That frees analysts to focus on strategic threats.”
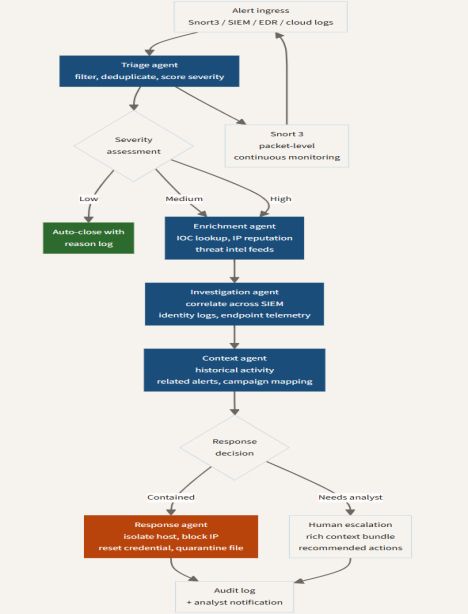
However, the move to agentic AI also raises new challenges. Autonomous agents must be explainable and accountable—if an agent makes a false blockade, who is responsible? Regulators and enterprises are calling for transparency in AI decision‑making.
Furthermore, the same AI technology can be used by attackers to craft adaptive evasion techniques, creating an arms race. Deep learning models are also data‑hungry and require extensive, high‑quality training sets to avoid biases.
Industry Reaction
Several vendors have already incorporated ML into their products. Cisco’s SecureX uses ML to correlate alerts, while Palo Alto Networks’ WildFire employs deep learning to analyze unknown files. But full agentic autonomy remains experimental.
“We’re seeing early adopters in finance and healthcare where the cost of missing an intrusion is catastrophic,” said Dr. Voss. “They are willing to trade off some predictability for higher detection rates.”
Market analysts predict that by 2028, over 70% of new IDS deployments will include at least some level of ML or agentic AI. The global IDS market is expected to grow from $4.5 billion to $8.2 billion, driven by this technological shift.
What’s Next?
The path forward involves hybrid systems that blend traditional signatures (for well‑known threats) with ML agents (for anomaly detection). Explainable AI (XAI) will become critical to trust in autonomous decisions.
As the industry races to adapt, one thing is clear: the sensor is no longer just a pattern matcher; it is learning, reasoning, and acting in real time.
This breaking news article was adapted from ongoing research in the field. Check back for updates as more organizations announce their migration to context‑aware intrusion detection.
Related Articles
- Navigating the New Era of Border Security Technology: A Guide to Autonomous and AI-Driven Solutions
- Yarbo Pledges Permanent Removal of Backdoor in Robot Lawn Mowers After Security Scare
- Maximize Your Fitness Tracking: How to Use Fitbit Air Alongside Your Pixel Watch
- Building a Context-Aware Intrusion Detection System: A Step-by-Step Guide to Implementing SnortML and Agentic AI
- Building a Resilient Validation Layer for Non-Deterministic AI Agents
- 7 Essential Steps to Launch a Successful Personalization Initiative
- Breaking: Dreame’s Smartphone Gamble—Modular Device Shown, Launch Uncertain
- Kickstart Your Personalization Strategy: A Step-by-Step Prepersonalization Workshop Guide